Setup steps for SSH connections to AWS CodeCommit repositories on Linux, macOS, or Unix
Before you can connect to CodeCommit for the first time, you must complete some initial configuration steps. After you set up your computer and AWS profile, you can connect to a CodeCommit repository and clone that repository to your computer (also known as creating a local repo). If you're new to Git, you might also want to review the information in Where can I learn more about Git?.
Topics
Step 1: Initial configuration for CodeCommit
Follow these steps to set up an Amazon Web Services account, create an IAM user, and configure access to CodeCommit.
To create and configure an IAM user for accessing CodeCommit
Create an Amazon Web Services account by going to http://aws.amazon.com
and choosing Sign Up. Create an IAM user, or use an existing one, in your Amazon Web Services account. Make sure you have an access key ID and a secret access key associated with that IAM user. For more information, see Creating an IAM User in Your Amazon Web Services account.
Note
CodeCommit requires AWS Key Management Service. If you are using an existing IAM user, make sure there are no policies attached to the user that expressly deny the AWS KMS actions required by CodeCommit. For more information, see AWS KMS and encryption.
Sign in to the AWS Management Console and open the IAM console at https://console.aws.amazon.com/iam/
. -
In the IAM console, in the navigation pane, choose Users, and then choose the IAM user you want to configure for CodeCommit access.
On the Permissions tab, choose Add Permissions.
-
In Grant permissions, choose Attach existing policies directly.
From the list of policies, select AWSCodeCommitPowerUser or another managed policy for CodeCommit access. For more information, see AWS managed policies for CodeCommit.
After you have selected the policy you want to attach, choose Next: Review to review the list of policies to attach to the IAM user. If the list is correct, choose Add permissions.
For more information about CodeCommit managed policies and sharing access to repositories with other groups and users, see Share a repository and Authentication and access control for AWS CodeCommit.
Note
If you want to use AWS CLI commands with CodeCommit, install the AWS CLI. For more information, see Command line reference.
Step 2: Install Git
To work with files, commits, and other information in CodeCommit repositories, you must install Git on your local machine. CodeCommit supports Git versions 1.7.9 and later. Git version 2.28 supports configuring the branch name for initial commits. We recommend using a recent version of Git.
To install Git, we recommend websites such as Git Downloads
Note
Git is an evolving, regularly updated platform. Occasionally, a feature change might affect the way it works with CodeCommit. If you encounter issues with a specific version of Git and CodeCommit, review the information in Troubleshooting.
Step 3: Configure credentials on Linux, macOS, or Unix
SSH and Linux, macOS, or Unix: Set up the public and private keys for Git and CodeCommit
To set up the public and private keys for Git and CodeCommit
-
From the terminal on your local machine, run the ssh-keygen command, and follow the directions to save the file to the .ssh directory for your profile.
Note
Be sure to check with your system administrator about where key files should be stored and which file naming pattern should be used.
For example:
$ ssh-keygen Generating public/private rsa key pair. Enter file in which to save the key (/home/user-name/.ssh/id_rsa):Type /home/your-user-name/.ssh/ and a file name here, for example /home/your-user-name/.ssh/codecommit_rsaEnter passphrase (empty for no passphrase):<Type a passphrase, and then press Enter>Enter same passphrase again:<Type the passphrase again, and then press Enter>Your identification has been saved in /home/user-name/.ssh/codecommit_rsa. Your public key has been saved in /home/user-name/.ssh/codecommit_rsa.pub. The key fingerprint is: 45:63:d5:99:0e:99:73:50:5e:d4:b3:2d:86:4a:2c:14user-name@client-nameThe key's randomart image is: +--[ RSA 2048]----+ | E.+.o*.++| | .o .=.=o.| | . .. *. +| | ..o . +..| | So . . . | | . | | | | | | | +-----------------+This generates:
-
The
codecommit_rsafile, which is the private key file. -
The
codecommit_rsa.pubfile, which is the public key file.
Tip
By default, ssh-keygen generates a 2048 bit key. You can use the -t and -b parameters to specify the type and length of the key. If you want a 4096 bit key in the rsa format, you would specify this by running the command with the following parameters:
ssh-keygen -t rsa -b 4096For more information about the formats and lengths required for SSH keys, see Using IAM with CodeCommit.
-
-
Run the following command to display the value of the public key file (
codecommit_rsa.pub):cat ~/.ssh/codecommit_rsa.pubCopy this value. It looks similar to the following:
ssh-rsa EXAMPLE-AfICCQD6m7oRw0uXOjANBgkqhkiG9w0BAQUFADCBiDELMAkGA1UEBhMCVVMxCzAJB gNVBAgTAldBMRAwDgYDVQQHEwdTZWF0dGxlMQ8wDQYDVQQKEwZBbWF6b24xFDASBgNVBAsTC0lBTSBDb2 5zb2xlMRIwEAYDVQQDEwlUZXN0Q2lsYWMxHzAdBgkqhkiG9w0BCQEWEG5vb25lQGFtYXpvbi5jb20wHhc NMTEwNDI1MjA0NTIxWhcNMTIwNDI0MjA0NTIxWjCBiDELMAkGA1UEBhMCVVMxCzAJBgNVBAgTAldBMRAw DgYDVQQHEwdTZWF0dGxlMQ8wDQYDVQQKEwZBbWF6b24xFDAS=EXAMPLEuser-name@ip-192-0-2-137 -
Sign in to the AWS Management Console and open the IAM console at https://console.aws.amazon.com/iam/
. Note
You can directly view and manage your CodeCommit credentials in My Security Credentials. For more information, see View and manage your credentials.
-
In the IAM console, in the navigation pane, choose Users, and from the list of users, choose your IAM user.
-
On the user details page, choose the Security Credentials tab, and then choose Upload SSH public key.
-
Paste the contents of your SSH public key into the field, and then choose Upload SSH public key.
-
Copy or save the information in SSH Key ID (for example,
APKAEIBAERJR2EXAMPLE).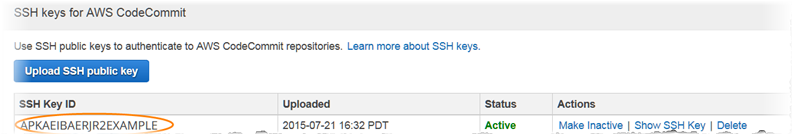
Note
If you have more than one SSH key IDs uploaded, the keys are listed alphabetically by key ID, not by upload date. Make sure that you have copied the key ID that is associated with the correct upload date.
-
On your local machine, use a text editor to create a config file in the ~/.ssh directory, and then add the following lines to the file, where the value for
Useris the SSH key ID you copied earlier:Host git-codecommit.*.amazonaws.com UserAPKAEIBAERJR2EXAMPLEIdentityFile ~/.ssh/codecommit_rsaNote
If you gave your private key file a name other than
codecommit_rsa, be sure to use it here.You can set up SSH access to repositories in multiple Amazon Web Services accounts, For more information, see Troubleshooting SSH connections to AWS CodeCommit.
Save and name this file
config. -
From the terminal, run the following command to change the permissions for the config file:
chmod 600 config -
Run the following command to test your SSH configuration:
ssh git-codecommit.us-east-2.amazonaws.comYou are asked to confirm the connection because
git-codecommit.us-east-2.amazonaws.comis not yet included in your known hosts file. The CodeCommit server fingerprint is displayed as part of the verification (a9:6d:03:ed:08:42:21:be:06:e1:e0:2a:d1:75:31:5efor MD5 or3lBlW2g5xn/NA2Ck6dyeJIrQOWvn7n8UEs56fG6ZIzQfor SHA256).Note
CodeCommit server fingerprints are unique for every AWS Region. To view the server fingerprints for an AWS Region, see Server fingerprints for CodeCommit.
After you have confirmed the connection, you should see confirmation that you have added the server to your known hosts file and a successful connection message. If you do not see a success message, check that you saved the
configfile in the ~/.ssh directory of the IAM user you configured for access to CodeCommit, and that you specified the correct private key file.For information to help you troubleshoot problems, run the
sshcommand with the-vparameter. For example:ssh -v git-codecommit.us-east-2.amazonaws.comFor information to help you troubleshoot connection problems, see Troubleshooting SSH connections to AWS CodeCommit.
Step 4: Connect to the CodeCommit console and clone the repository
If an administrator has already sent you the name and connection details for the CodeCommit repository, you can skip this step and clone the repository directly.
To connect to a CodeCommit repository
Open the CodeCommit console at https://console.aws.amazon.com/codesuite/codecommit/home
. -
In the region selector, choose the AWS Region where the repository was created. Repositories are specific to an AWS Region. For more information, see Regions and Git connection endpoints.
-
Find the repository you want to connect to from the list and choose it. Choose Clone URL, and then choose the protocol you want to use when cloning or connecting to the repository. This copies the clone URL.
Copy the HTTPS URL if you are using either Git credentials with your IAM user or the credential helper included with the AWS CLI.
Copy the HTTPS (GRC) URL if you are using the git-remote-codecommit command on your local computer.
Copy the SSH URL if you are using an SSH public/private key pair with your IAM user.
Note
If you see a Welcome page instead of a list of repositories, there are no repositories associated with your AWS account in the AWS Region where you are signed in. To create a repository, see Create an AWS CodeCommit repository or follow the steps in the Getting started with Git and CodeCommit tutorial.
-
Open a terminal. From the /tmp directory, run the git clone command with the SSH URL you copied to clone the repository. For example, to clone a repository named
MyDemoRepoto a local repo namedmy-demo-repoin the US East (Ohio) Region:git clone ssh://git-codecommit.us-east-2.amazonaws.com/v1/repos/MyDemoRepo my-demo-repoNote
If you successfully tested your connection, but the clone command fails, you might not have the required access to your config file, or another setting might be in conflict with your config file. Try connecting again, this time including the SSH key ID in the command. For example:
git clone ssh://Your-SSH-Key-ID@git-codecommit.us-east-2.amazonaws.com/v1/repos/MyDemoRepo my-demo-repoFor more information, see Access error: Public key is uploaded successfully to IAM but connection fails on Linux, macOS, or Unix systems.
For more information about how to connect to repositories, see Connect to the CodeCommit repository by cloning the repository.
Next steps
You have completed the prerequisites. Follow the steps in Getting started with CodeCommit to start using CodeCommit.