Troubleshooting AWS Account Management identity and access
Use the following information to help you diagnose and fix common issues that you might encounter when working with Account Management and IAM.
Topics
I am not authorized to perform an action in the Account page
If the AWS Management Console tells you that you're not authorized to perform an action, then you must contact your administrator for assistance. Your administrator is the person that provided you with your user name and password.
The following example error occurs when the mateojackson IAM user
tries to use the console to view details about his AWS account in the
Account page of the AWS Management Console but doesn't have the
account:GetAccountInformation permissions.
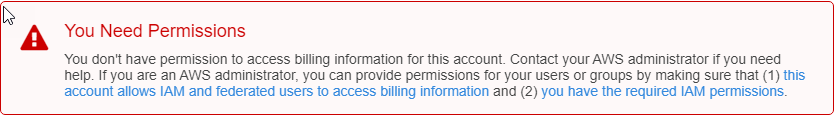
In this case, Mateo asks his administrator to update his policies to allow him to
access the my-example-widgetaccount: action.GetWidget
I am not authorized to perform
iam:PassRole
If you receive an error that you're not authorized to perform the iam:PassRole action, your policies must be updated to allow you to pass a role to Account Management.
Some AWS services allow you to pass an existing role to that service instead of creating a new service role or service-linked role. To do this, you must have permissions to pass the role to the service.
The following example error occurs when an IAM user named marymajor tries to use the console to perform an action in
Account Management. However, the action requires the service to have permissions that are granted by a service role. Mary does not have permissions to pass the
role to the service.
User: arn:aws:iam::123456789012:user/marymajoris not authorized to perform: iam:PassRole
In this case, Mary's policies must be updated to allow her to perform the iam:PassRole action.
If you need help, contact your AWS administrator. Your administrator is the person who provided you with your sign-in credentials.
I want to allow people outside of my AWS account to access my account details
You can create a role that users in other accounts or people outside of your organization can use to access your resources. You can specify who is trusted to assume the role. For services that support resource-based policies or access control lists (ACLs), you can use those policies to grant people access to your resources.
To learn more, consult the following:
-
To learn whether Account Management supports these features, see How AWS Account Management works with IAM.
-
To learn how to provide access to your resources across AWS accounts that you own, see Providing access to an IAM user in another AWS account that you own in the IAM User Guide.
-
To learn how to provide access to your resources to third-party AWS accounts, see Providing access to AWS accounts owned by third parties in the IAM User Guide.
-
To learn how to provide access through identity federation, see Providing access to externally authenticated users (identity federation) in the IAM User Guide.
-
To learn the difference between using roles and resource-based policies for cross-account access, see Cross account resource access in IAM in the IAM User Guide.