Terjemahan disediakan oleh mesin penerjemah. Jika konten terjemahan yang diberikan bertentangan dengan versi bahasa Inggris aslinya, utamakan versi bahasa Inggris.
Gunakan tindakan AWS FIS aws:ecs:task
Anda dapat menggunakan tindakan aws:ecs:task untuk menyuntikkan kesalahan ke dalam tugas Amazon ECS Anda. Jenis kapasitas Amazon EC2 dan Fargate didukung.
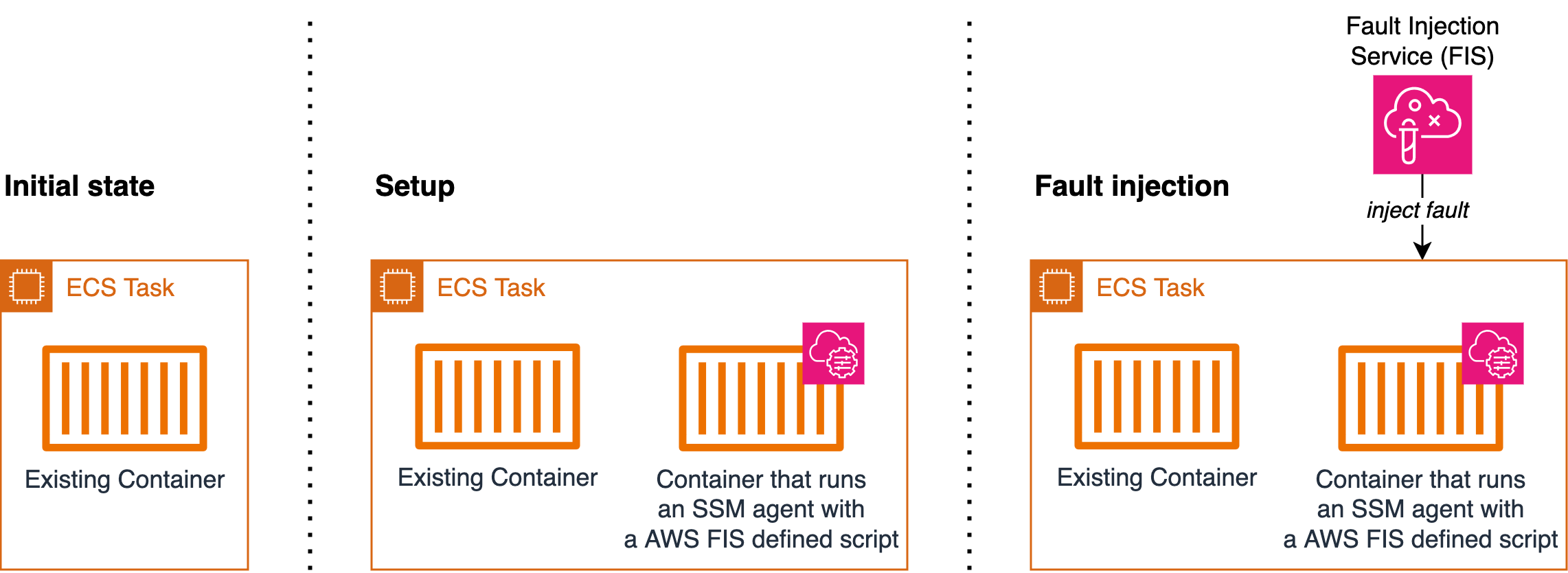
Tindakan ini menggunakan dokumen AWS Systems Manager (SSM) untuk menyuntikkan kesalahan. Untuk menggunakan aws:ecs:task tindakan, Anda perlu menambahkan kontainer dengan Agen SSM ke definisi tugas Amazon Elastic Container Service (Amazon ECS) Container Service (Amazon ECS). Container menjalankan skrip yang AWS ditentukan FIS yang mendaftarkan tugas Amazon ECS sebagai Instans Terkelola dalam layanan SSM. Selain itu, skrip mengambil metadata tugas untuk menambahkan tag ke Instans Terkelola. Pengaturan akan memungkinkan AWS FIS untuk menyelesaikan tugas target. Paragraf ini mengacu pada Setup pada diagram di bawah ini.
Saat Anda menjalankan penargetan eksperimen AWS FISaws:ecs:task, AWS FIS memetakan tugas Amazon ECS target yang Anda tentukan dalam templat eksperimen AWS FIS ke sekumpulan instance terkelola SSM menggunakan tag sumber daya. ECS_TASK_ARN Nilai tag adalah ARN dari tugas Amazon ECS terkait di mana dokumen SSM harus dijalankan. Paragraf ini mengacu pada Injeksi Kesalahan pada diagram di bawah ini.
Diagram berikut mencontohkan pengaturan dan injeksi kesalahan pada tugas dengan satu wadah yang ada.
Tindakan
Batasan
-
Tindakan berikut tidak dapat berjalan secara paralel:
aws:ecs:task-network-blackhole-port
aws:ecs:task-network-latency
aws:ecs:task-network-packet-loss
-
Jika Anda mengaktifkan Amazon ECS Exec, Anda harus menonaktifkannya sebelum dapat menggunakan tindakan ini.
-
Eksekusi dokumen SSM mungkin memiliki Status Dibatalkan bahkan jika eksperimen memiliki Status Selesai. Saat menjalankan tindakan Amazon ECS, durasi yang disediakan pelanggan digunakan baik untuk durasi tindakan dalam eksperimen maupun durasi dokumen Amazon EC2 Systems Manager (SSM). Setelah tindakan dimulai, dibutuhkan beberapa waktu untuk dokumen SSM untuk mulai berjalan. Akibatnya, pada saat durasi tindakan yang ditentukan tercapai, dokumen SSM mungkin masih memiliki beberapa detik tersisa untuk menyelesaikan pelaksanaannya. Ketika durasi tindakan percobaan tercapai, tindakan dihentikan, dan eksekusi dokumen SSM dibatalkan. Injeksi kesalahan berhasil.
Persyaratan
-
Tambahkan izin berikut ke peran eksperimen AWS FIS:
ecs:DescribeTasksssm:SendCommandssm:ListCommandsssm:CancelCommand
-
Tambahkan izin berikut ke peran IAM tugas Amazon ECS:
ssm:CreateActivationssm:AddTagsToResourceiam:PassRole
Perhatikan bahwa Anda dapat menentukan ARN dari peran instans terkelola sebagai sumber daya untuk.
iam:PassRole -
Buat peran IAM eksekusi tugas Amazon ECS dan tambahkan kebijakan ECSTask ExecutionRolePolicy terkelola Amazon.
-
Dalam definisi tugas, atur variabel lingkungan
MANAGED_INSTANCE_ROLE_NAMEke nama peran instance terkelola. Ini adalah peran yang akan dilampirkan pada tugas yang terdaftar sebagai instance terkelola di SSM. -
Tambahkan izin berikut ke peran instans terkelola:
ssm:DeleteActivationssm:DeregisterManagedInstance
-
Tambahkan kebijakan SSMManaged InstanceCore terkelola Amazon ke peran instans terkelola.
-
Tambahkan wadah agen SSM ke definisi tugas Amazon ECS. Skrip perintah mendaftarkan tugas Amazon ECS sebagai instance terkelola.
{ "name": "amazon-ssm-agent", "image": "public.ecr.aws/amazon-ssm-agent/amazon-ssm-agent:latest", "cpu": 0, "links": [], "portMappings": [], "essential": false, "entryPoint": [], "command": [ "/bin/bash", "-c", "set -e; dnf upgrade -y; dnf install jq procps awscli -y; term_handler() { echo \"Deleting SSM activation $ACTIVATION_ID\"; if ! aws ssm delete-activation --activation-id $ACTIVATION_ID --region $ECS_TASK_REGION; then echo \"SSM activation $ACTIVATION_ID failed to be deleted\" 1>&2; fi; MANAGED_INSTANCE_ID=$(jq -e -r .ManagedInstanceID /var/lib/amazon/ssm/registration); echo \"Deregistering SSM Managed Instance $MANAGED_INSTANCE_ID\"; if ! aws ssm deregister-managed-instance --instance-id $MANAGED_INSTANCE_ID --region $ECS_TASK_REGION; then echo \"SSM Managed Instance $MANAGED_INSTANCE_ID failed to be deregistered\" 1>&2; fi; kill -SIGTERM $SSM_AGENT_PID; }; trap term_handler SIGTERM SIGINT; if [[ -z $MANAGED_INSTANCE_ROLE_NAME ]]; then echo \"Environment variable MANAGED_INSTANCE_ROLE_NAME not set, exiting\" 1>&2; exit 1; fi; if ! ps ax | grep amazon-ssm-agent | grep -v grep > /dev/null; then if [[ -n $ECS_CONTAINER_METADATA_URI_V4 ]] ; then echo \"Found ECS Container Metadata, running activation with metadata\"; TASK_METADATA=$(curl \"${ECS_CONTAINER_METADATA_URI_V4}/task\"); ECS_TASK_AVAILABILITY_ZONE=$(echo $TASK_METADATA | jq -e -r '.AvailabilityZone'); ECS_TASK_ARN=$(echo $TASK_METADATA | jq -e -r '.TaskARN'); ECS_TASK_REGION=$(echo $ECS_TASK_AVAILABILITY_ZONE | sed 's/.$//'); ECS_TASK_AVAILABILITY_ZONE_REGEX='^(af|ap|ca|cn|eu|me|sa|us|us-gov)-(central|north|(north(east|west))|south|south(east|west)|east|west)-[0-9]{1}[a-z]{1}$'; if ! [[ $ECS_TASK_AVAILABILITY_ZONE =~ $ECS_TASK_AVAILABILITY_ZONE_REGEX ]]; then echo \"Error extracting Availability Zone from ECS Container Metadata, exiting\" 1>&2; exit 1; fi; ECS_TASK_ARN_REGEX='^arn:(aws|aws-cn|aws-us-gov):ecs:[a-z0-9-]+:[0-9]{12}:task/[a-zA-Z0-9_-]+/[a-zA-Z0-9]+$'; if ! [[ $ECS_TASK_ARN =~ $ECS_TASK_ARN_REGEX ]]; then echo \"Error extracting Task ARN from ECS Container Metadata, exiting\" 1>&2; exit 1; fi; CREATE_ACTIVATION_OUTPUT=$(aws ssm create-activation --iam-role $MANAGED_INSTANCE_ROLE_NAME --tags Key=ECS_TASK_AVAILABILITY_ZONE,Value=$ECS_TASK_AVAILABILITY_ZONE Key=ECS_TASK_ARN,Value=$ECS_TASK_ARN Key=FAULT_INJECTION_SIDECAR,Value=true --region $ECS_TASK_REGION); ACTIVATION_CODE=$(echo $CREATE_ACTIVATION_OUTPUT | jq -e -r .ActivationCode); ACTIVATION_ID=$(echo $CREATE_ACTIVATION_OUTPUT | jq -e -r .ActivationId); if ! amazon-ssm-agent -register -code $ACTIVATION_CODE -id $ACTIVATION_ID -region $ECS_TASK_REGION; then echo \"Failed to register with AWS Systems Manager (SSM), exiting\" 1>&2; exit 1; fi; amazon-ssm-agent & SSM_AGENT_PID=$!; wait $SSM_AGENT_PID; else echo \"ECS Container Metadata not found, exiting\" 1>&2; exit 1; fi; else echo \"SSM agent is already running, exiting\" 1>&2; exit 1; fi" ], "environment": [ { "name": "MANAGED_INSTANCE_ROLE_NAME", "value": "SSMManagedInstanceRole" } ], "environmentFiles": [], "mountPoints": [], "volumesFrom": [], "secrets": [], "dnsServers": [], "dnsSearchDomains": [], "extraHosts": [], "dockerSecurityOptions": [], "dockerLabels": {}, "ulimits": [], "logConfiguration": {}, "systemControls": [] }Untuk versi skrip yang lebih mudah dibaca, lihatVersi referensi skrip.
-
Aktifkan Injeksi Kesalahan Amazon ECS APIs, dengan menyetel
enableFaultInjectionbidang dalam definisi tugas Amazon ECS:"enableFaultInjection": true, -
Saat menggunakan
aws:ecs:task-network-blackhole-port,aws:ecs:task-network-latency, atauaws:ecs:task-network-packet-losstindakan pada tugas Fargate, tindakan harus memilikiuseEcsFaultInjectionEndpointsparameter yang disetel ke.true -
Saat menggunakan
aws:ecs:task-kill-process,,aws:ecs:task-network-blackhole-portaws:ecs:task-network-latency, danaws:ecs:task-network-packet-losstindakan, definisi tugas Amazon ECS haruspidModedisetel ketask. -
Saat menggunakan
aws:ecs:task-network-blackhole-port,aws:ecs:task-network-latency, danaws:ecs:task-network-packet-losstindakan, definisi tugas Amazon ECS harusnetworkModedisetel ke nilai selainbridge.
Versi referensi skrip
Berikut ini adalah versi skrip yang lebih mudah dibaca di bagian Persyaratan, untuk referensi Anda.
#!/usr/bin/env bash # This is the activation script used to register ECS tasks as Managed Instances in SSM # The script retrieves information form the ECS task metadata endpoint to add three tags to the Managed Instance # - ECS_TASK_AVAILABILITY_ZONE: To allow customers to target Managed Instances / Tasks in a specific Availability Zone # - ECS_TASK_ARN: To allow customers to target Managed Instances / Tasks by using the Task ARN # - FAULT_INJECTION_SIDECAR: To make it clear that the tasks were registered as managed instance for fault injection purposes. Value is always 'true'. # The script will leave the SSM Agent running in the background # When the container running this script receives a SIGTERM or SIGINT signal, it will do the following cleanup: # - Delete SSM activation # - Deregister SSM managed instance set -e # stop execution instantly as a query exits while having a non-zero dnf upgrade -y dnf install jq procps awscli -y term_handler() { echo "Deleting SSM activation $ACTIVATION_ID" if ! aws ssm delete-activation --activation-id $ACTIVATION_ID --region $ECS_TASK_REGION; then echo "SSM activation $ACTIVATION_ID failed to be deleted" 1>&2 fi MANAGED_INSTANCE_ID=$(jq -e -r .ManagedInstanceID /var/lib/amazon/ssm/registration) echo "Deregistering SSM Managed Instance $MANAGED_INSTANCE_ID" if ! aws ssm deregister-managed-instance --instance-id $MANAGED_INSTANCE_ID --region $ECS_TASK_REGION; then echo "SSM Managed Instance $MANAGED_INSTANCE_ID failed to be deregistered" 1>&2 fi kill -SIGTERM $SSM_AGENT_PID } trap term_handler SIGTERM SIGINT # check if the required IAM role is provided if [[ -z $MANAGED_INSTANCE_ROLE_NAME ]] ; then echo "Environment variable MANAGED_INSTANCE_ROLE_NAME not set, exiting" 1>&2 exit 1 fi # check if the agent is already running (it will be if ECS Exec is enabled) if ! ps ax | grep amazon-ssm-agent | grep -v grep > /dev/null; then # check if ECS Container Metadata is available if [[ -n $ECS_CONTAINER_METADATA_URI_V4 ]] ; then # Retrieve info from ECS task metadata endpoint echo "Found ECS Container Metadata, running activation with metadata" TASK_METADATA=$(curl "${ECS_CONTAINER_METADATA_URI_V4}/task") ECS_TASK_AVAILABILITY_ZONE=$(echo $TASK_METADATA | jq -e -r '.AvailabilityZone') ECS_TASK_ARN=$(echo $TASK_METADATA | jq -e -r '.TaskARN') ECS_TASK_REGION=$(echo $ECS_TASK_AVAILABILITY_ZONE | sed 's/.$//') # validate ECS_TASK_AVAILABILITY_ZONE ECS_TASK_AVAILABILITY_ZONE_REGEX='^(af|ap|ca|cn|eu|me|sa|us|us-gov)-(central|north|(north(east|west))|south|south(east|west)|east|west)-[0-9]{1}[a-z]{1}$' if ! [[ $ECS_TASK_AVAILABILITY_ZONE =~ $ECS_TASK_AVAILABILITY_ZONE_REGEX ]] ; then echo "Error extracting Availability Zone from ECS Container Metadata, exiting" 1>&2 exit 1 fi # validate ECS_TASK_ARN ECS_TASK_ARN_REGEX='^arn:(aws|aws-cn|aws-us-gov):ecs:[a-z0-9-]+:[0-9]{12}:task/[a-zA-Z0-9_-]+/[a-zA-Z0-9]+$' if ! [[ $ECS_TASK_ARN =~ $ECS_TASK_ARN_REGEX ]] ; then echo "Error extracting Task ARN from ECS Container Metadata, exiting" 1>&2 exit 1 fi # Create activation tagging with Availability Zone and Task ARN CREATE_ACTIVATION_OUTPUT=$(aws ssm create-activation \ --iam-role $MANAGED_INSTANCE_ROLE_NAME \ --tags Key=ECS_TASK_AVAILABILITY_ZONE,Value=$ECS_TASK_AVAILABILITY_ZONE Key=ECS_TASK_ARN,Value=$ECS_TASK_ARN Key=FAULT_INJECTION_SIDECAR,Value=true \ --region $ECS_TASK_REGION) ACTIVATION_CODE=$(echo $CREATE_ACTIVATION_OUTPUT | jq -e -r .ActivationCode) ACTIVATION_ID=$(echo $CREATE_ACTIVATION_OUTPUT | jq -e -r .ActivationId) # Register with AWS Systems Manager (SSM) if ! amazon-ssm-agent -register -code $ACTIVATION_CODE -id $ACTIVATION_ID -region $ECS_TASK_REGION; then echo "Failed to register with AWS Systems Manager (SSM), exiting" 1>&2 exit 1 fi # the agent needs to run in the background, otherwise the trapped signal # won't execute the attached function until this process finishes amazon-ssm-agent & SSM_AGENT_PID=$! # need to keep the script alive, otherwise the container will terminate wait $SSM_AGENT_PID else echo "ECS Container Metadata not found, exiting" 1>&2 exit 1 fi else echo "SSM agent is already running, exiting" 1>&2 exit 1 fi
Contoh template percobaan
Berikut ini adalah contoh template eksperimen untuk aws:ecs:task-cpu-stress tindakan tersebut.
{ "description": "Run CPU stress on the target ECS tasks", "targets": { "myTasks": { "resourceType": "aws:ecs:task", "resourceArns": [ "arn:aws:ecs:us-east-1:111122223333:task/my-cluster/09821742c0e24250b187dfed8EXAMPLE" ], "selectionMode": "ALL" } }, "actions": { "EcsTask-cpu-stress": { "actionId": "aws:ecs:task-cpu-stress", "parameters": { "duration": "PT1M" }, "targets": { "Tasks": "myTasks" } } }, "stopConditions": [ { "source": "none", } ], "roleArn": "arn:aws:iam::111122223333:role/fis-experiment-role", "tags": {} }