翻訳は機械翻訳により提供されています。提供された翻訳内容と英語版の間で齟齬、不一致または矛盾がある場合、英語版が優先します。
Amazon EC2 Windows インスタンスを AWS Managed Microsoft AD に結合する Active Directory
Amazon EC2 Windowsインスタンスを起動して AWS Managed Microsoft AD に参加できます。または、既存の EC2 Windowsインスタンスを AWS Managed Microsoft AD に手動で結合することもできます。
- Seamlessly join EC2 Windows instance
-
この手順では、Amazon EC2 Windowsインスタンスを AWS Managed Microsoft AD にシームレスに結合します。複数の でシームレスなドメイン結合を実行する必要がある場合は AWS アカウント、「」を参照してくださいチュートリアル: AWS Managed Microsoft AD ディレクトリを共有してシームレスな EC2 ドメイン結合を実現する。Amazon EC2 の詳細については、「Amazon EC2 とは」を参照してください。
前提条件
EC2 インスタンスをシームレスにドメイン結合するには、以下を完了する必要があります。
-
AWS Managed Microsoft AD がある。詳細についてはAWS Managed Microsoft AD の作成を参照してください。
-
EC2 Windowsインスタンスをシームレスに結合するには、次の IAM アクセス許可が必要です。
-
次の IAM アクセス許可を持つ IAM インスタンスプロファイル:
-
AmazonSSMManagedInstanceCore -
AmazonSSMDirectoryServiceAccess
-
-
EC2 を AWS Managed Microsoft AD にシームレスに結合するユーザーには、次の IAM アクセス許可が必要です。
-
AWS Directory Service アクセス許可:
-
"ds:DescribeDirectories" -
"ds:CreateComputer"
-
-
Amazon VPC のアクセス許可:
-
"ec2:DescribeVpcs" -
"ec2:DescribeSubnets" -
"ec2:DescribeNetworkInterfaces" -
"ec2:CreateNetworkInterface" -
"ec2:AttachNetworkInterface"
-
-
EC2 アクセス許可:
-
"ec2:DescribeInstances" -
"ec2:DescribeImages" -
"ec2:DescribeInstanceTypes" -
"ec2:RunInstances" -
"ec2:CreateTags"
-
-
AWS Systems Manager アクセス許可:
-
"ssm:DescribeInstanceInformation" -
"ssm:SendCommand" -
"ssm:GetCommandInvocation" -
"ssm:CreateBatchAssociation"
-
-
-
AWS Managed Microsoft AD が作成されると、インバウンドルールとアウトバウンドルールを使用してセキュリティグループが作成されます。これらのルールとポートの詳細については、「」を参照してくださいAWS Managed Microsoft AD で作成されるもの。EC2 Windowsインスタンスをシームレスにドメイン結合するには、インスタンスを起動する VPC で、 AWS Managed Microsoft AD セキュリティグループのインバウンドルールとアウトバウンドルールで許可されているのと同じポートを許可する必要があります。
-
ネットワークセキュリティとファイアウォールの設定によっては、追加のアウトバウンドトラフィックを許可する必要がある場合があります。このトラフィックは、次のエンドポイントへの HTTPS (ポート 443) 用になります。
Endpoint ロール ec2messages.region.amazonaws.comSession Manager サービスを使用してセッションチャネルを作成および削除します。詳細については、「AWS Systems Manager エンドポイントとクォータ」を参照してください。
ssm.region.amazonaws.comのエンドポイント AWS Systems Manager Session Manager。詳細については、「AWS Systems Manager エンドポイントとクォータ」を参照してください。
ssmmessages.region.amazonaws.comSession Manager サービスを使用してセッションチャネルを作成および削除します。詳細については、「AWS Systems Manager エンドポイントとクォータ」を参照してください。
ds.region.amazonaws.comのエンドポイント AWS Directory Service。詳細については、「のリージョンの可用性 AWS Directory Service」を参照してください。
-
AWS Managed Microsoft AD ドメイン名を解決する DNS サーバーを使用することをお勧めします。そのためには、DHCP オプションセットを作成できます。詳細については「AWS Managed Microsoft AD の DHCP オプションセットの作成または変更」を参照してください。
-
DHCP オプションセットを作成しない場合、DNS サーバーは静的になり、 AWS Managed Microsoft AD によって に設定されます。
-
Amazon EC2 Windows インスタンスをシームレスに結合するには
-
にサインイン AWS Management Console し、https://console.aws.amazon.com/ec2/
で Amazon EC2 コンソールを開きます。 -
ナビゲーションバーで、既存のディレクトリ AWS リージョン と同じ を選択します。
-
[EC2 ダッシュボード] の [インスタンスを起動する] セクションで、[インスタンスを起動する] を選択します。
-
[インスタンスを起動する] ページの [名前とタグ] セクションで、Windows EC2 インスタンスに使用する名前を入力します。
(オプション) [補足タグを追加] で、タグとキーの値のペアを 1 つまたは複数追加して、この EC2 インスタンスのアクセスを整理、追跡、または制御します。
-
[アプリケーションと OS イメージ (Amazon マシンイメージ)] セクションの [クイックスタート] ペインで [Windows] を選択します。Windows Amazon マシンイメージ (AMI) は、[Amazon マシンイメージ (AMI)] ドロップダウンリストから変更できます。
-
[インスタンスタイプ] セクションで、[インスタンスタイプ] ドロップダウンリストから使用するインスタンスタイプを選択します。
-
[キーペア (ログイン)] セクションで、新しいキーペアを作成するか、既存のキーペアから選択します。
新しいキーペアを作成するには、[新しいキーペアの作成] を選択します。
キーペアの名前を入力し、[キーペアタイプ] と [プライベートキーファイル形式] のオプションを選択します。
OpenSSH で使用できる形式でプライベートキーを保存するには、[.pem] を選択します。プライベートキーを PuTTY で使用できる形式で保存するには、[.ppk] を選択します。
[キーペアの作成] を選択します。
ブラウザによって秘密キーファイルが自動的にダウンロードされます。ダウンロードしたプライベートキーのファイルを安全な場所に保存します。
重要
プライベートキーのファイルを保存できるのはこのタイミングだけです。
-
[インスタンスを起動する] ページの [ネットワーク設定] セクションで、[編集] を選択します。[VPC に必須の] ドロップダウンリストから、ディレクトリが作成された [VPC] を選択します。
-
[サブネット] ドロップダウンリストから VPC 内のパブリックサブネットの 1 つを選択します。選択するサブネットで、すべての外部トラフィックがインターネットゲートウェイにルーティングされるように選択する必要があります。そうでない場合は、インスタンスにリモート接続できません。
インターネットゲートウェイへの接続方法の詳細については、Amazon VPC ユーザーガイドの「インターネットゲートウェイを使用してサブネットをインターネットに接続する」を参照してください。
-
[自動割り当てパブリック IP] で、[有効化] を選択します。
公開 IP アドレス指定とプライベート IP アドレス指定の詳細については、「Amazon EC2 インスタンスユーザーガイド」の「Amazon EC2 インスタンスの IP アドレス指定」を参照してください。
-
[ファイアウォール (セキュリティグループ)] 設定にはデフォルト設定を使用するか、必要に応じて変更を加えることができます。
-
[ストレージの設定] 設定にはデフォルト設定を使用するか、必要に応じて変更を加えることができます。
-
[高度な詳細] セクションを選択し、[ドメイン結合ディレクトリ] ドロップダウンリストからドメインを選択します。
注記
ドメイン結合ディレクトリを選択すると、次のようになります:
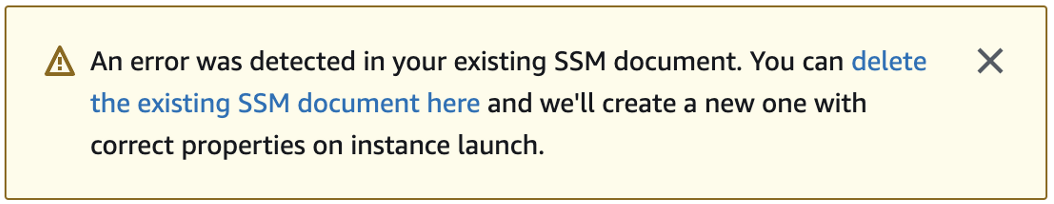
このエラーは、EC2 起動ウィザードが予期しないプロパティを持つ既存の SSM ドキュメントを識別した場合に発生します。次のいずれかを試すことができます。
以前に SSM ドキュメントを編集し、プロパティの存在が予想される場合は、[閉じる] を選択して EC2 インスタンスを変更せずに起動します。
ここで既存の SSM ドキュメントを削除するリンクを選択して、SSM ドキュメントを削除します。これにより、正しいプロパティを使用する SSM ドキュメントを作成できます。EC2 インスタンスを起動すると、SSM ドキュメントが自動的に作成されます。
-
[IAM インスタンスプロファイル] には既存の IAM インスタンスプロファイルを選択するか、新しいプロファイルを作成できます。管理 AWS ポリシー AmazonSSMManagedInstanceCore と AmazonSSMDirectoryServiceAccess がアタッチされている IAM インスタンスプロファイルを IAM インスタンスプロファイルドロップダウンリストから選択します。新しい IAM プロファイルリンクを作成するには、[新しい IAM プロファイルを作成する] リンクを選択し、以下を実行します。
-
[ロールの作成] を選択してください。
-
[Select trusted entity] (信頼されたエンティティを選択) で、[AWS サービス] を選択します。
-
[ユースケース] で、[EC2] を選択してください。
-
ポリシーのリスト内の [アクセス許可を追加する] の下で、AmazonSSMManagedInstanceCore ポリシーと AmazonSSMDirectoryServiceAccess ポリシーを選択します。リストを絞り込むため、検索ボックスに
SSMと入力します。[次へ] を選択します。注記
AmazonSSMDirectoryServiceAccess は、 によってActive Directory管理される にインスタンスを結合するアクセス許可を提供します AWS Directory Service。AmazonSSMManagedInstanceCore は、 AWS Systems Manager サービスを使用するために必要な最小限のアクセス許可を提供します。これらのアクセス許可を使用してロールを作成する方法、および IAM ロールに割り当てることができるその他のアクセス許可とポリシーの詳細については、「AWS Systems Manager ユーザーガイド」の「Systems Manager の IAM インスタンスプロファイルを作成する」を参照してください。
-
[名前、確認、作成] ページで、[ロール名] を入力します。EC2 インスタンスにアタッチするには、このロール名が必要です。
-
(オプション) IAM インスタンスプロファイルの説明を [説明] フィールドに入力できます。
-
[ロールの作成] を選択してください。
-
[インスタンスを起動する] ページに戻り、[IAM インスタンスプロファイル] の横にある更新アイコンを選択します。新しい IAM インスタンスプロファイルが [IAM インスタンスプロファイル] ドロップダウンリストに表示されるはずです。新しいプロファイルを選択し、残りの設定はデフォルト値のままにします。
-
-
[インスタンスを起動] を選択します。
-
- Manually join EC2 Windows instance
既存の Amazon EC2 Windows インスタンスを AWS Managed Microsoft AD Active Directory に手動で結合するには、Amazon EC2 Windows インスタンスを AWS Managed Microsoft AD に結合する Active Directory で指定したパラメータを使用して、インスタンスを起動する必要があります。
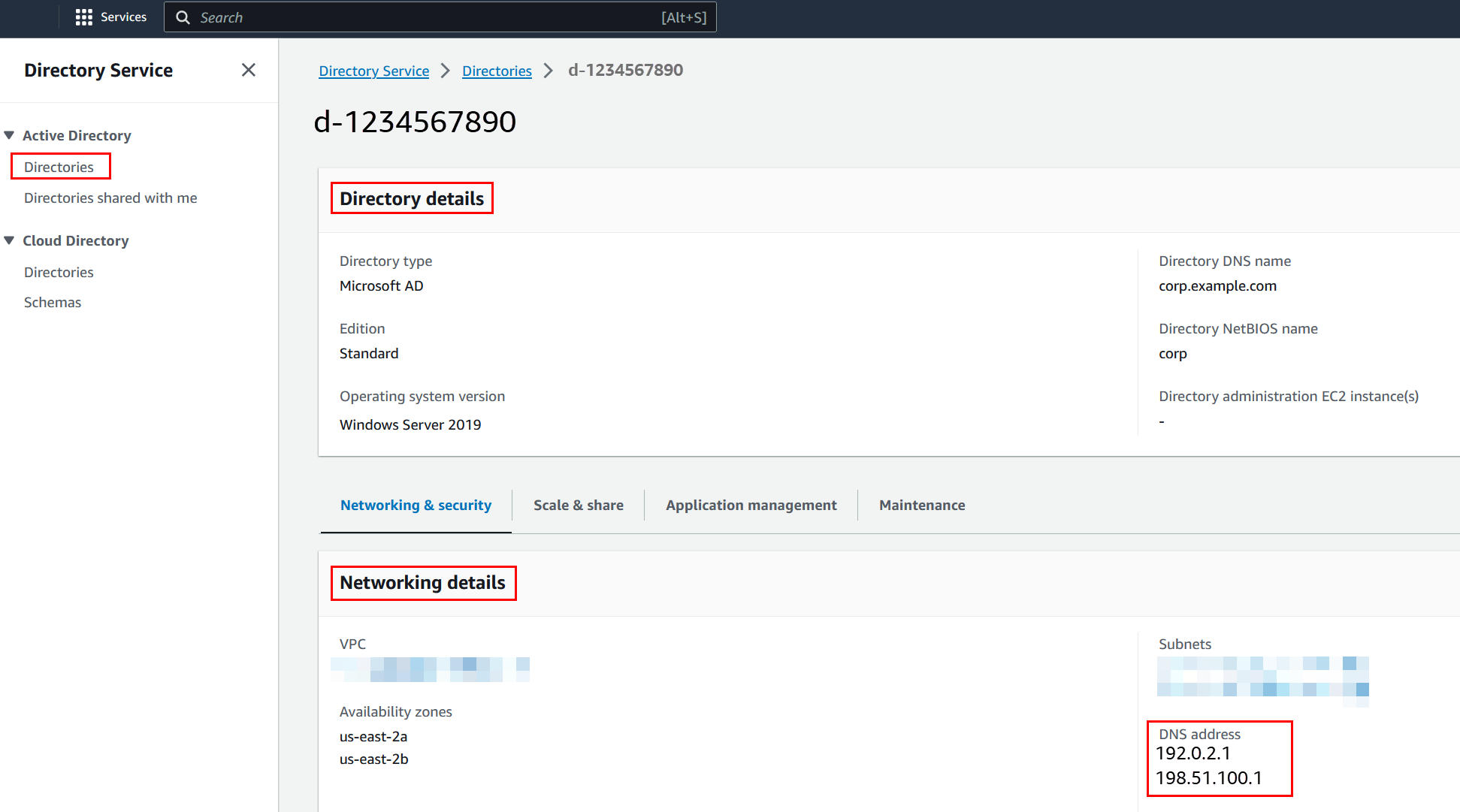
AWS Managed Microsoft AD DNS サーバーの IP アドレスが必要です。この情報は、お使いのディレクトリ > [ディレクトリの詳細] セクションと [ネットワークとセキュリティ] セクションの、[ディレクトリサービス] > [ディレクトリ] > [ディレクトリ ID] リンクの下にあります。
Windows インスタンスを AWS Managed Microsoft AD に結合するには Active Directory
-
リモートデスクトッププロトコルクライアントを使用してインスタンスに接続します。
-
インスタンスの TCP / IPv4 プロパティダイアログボックスを開きます。
-
ネットワーク接続を開きます。
ヒント
インスタンスのコマンドプロンプトから以下のコマンドを実行すると、[Network Connections] (ネットワーク接続) を直接開くことができます。
%SystemRoot%\system32\control.exe ncpa.cpl -
有効になっているネットワーク接続のコンテキストメニュー (右クリック) を開き、[Properties] (プロパティ) を選択します。
-
接続のプロパティダイアログボックスで、[Internet Protocol Version 4] をダブルクリックして開きます。
-
-
選択 次の DNS サーバーアドレスを使用し、優先 DNS サーバーと代替 DNS サーバーのアドレスを AWS Managed Microsoft AD 提供の DNS サーバーの IP アドレスに変更し、OK を選択します。
![[Internet Protocol Version 4 (TCP/IPv4) Properties] ダイアログボックスの [Properties] ダイアログボックスでは、[優先 DNS サーバー] フィールドと [Alternative] フィールドが強調表示されています。](images/dns_server_addresses.png)
-
インスタンスの [System Properties] (システムプロパティ) ダイアログボックスを開き、[Computer Name] (コンピュータ名) タブを選択して、[Change] (変更) をクリックします。
ヒント
インスタンスのコマンドプロンプトから以下のコマンドを実行すると、[System Properties] (システムプロパティ) ダイアログボックスを直接開くことができます。
%SystemRoot%\system32\control.exe sysdm.cpl -
フィールドのメンバーで、ドメインを選択し、 AWS Managed Microsoft AD Active Directory の完全修飾名を入力し、OK を選択します。
-
ドメイン管理者の名前とパスワードの入力を求められたら、ドメイン結合権限を持つアカウントのユーザー名とパスワードを入力します。これらの権限の委任に関する詳細については、「AWS Managed Microsoft AD のディレクトリ結合権限を委任する」を参照してください。
注記
ドメインの完全修飾名または NetBIOS 名のいずれかを入力できます。これに続けて、バックスラッシュ (\)、ユーザー名の順に入力します。ユーザー名は [Admin] になります。例えば、
corp.example.com\admin、corp\adminです。 -
ドメインへのアクセスを歓迎するメッセージを受け取ったら、インスタンスを再起動して変更を有効にします。
インスタンスが AWS Managed Microsoft AD Active Directory ドメインに結合されたので、そのインスタンスにリモートでログインし、ユーザーやグループの追加など、ディレクトリを管理するユーティリティをインストールできます。Active Directory 管理ツールを使用して、ユーザーとグループを作成できます。詳細については、「AWS Managed Microsoft AD 用の Active Directory 管理ツールのインストール」を参照してください。
注記
Amazon EC2 インスタンスの DNS アドレスを手動で変更する代わりに、Amazon Route 53 を使用して DNS クエリを処理することもできます。詳細については、「Directory Service の DNS 解決策を Amazon Route 53 Resolverと統合する
」および「アウトバウンド DNS クエリをネットワークに転送する」を参照してください。 -