This whitepaper is for historical reference only. Some content might be outdated and some links might not be available.
Applications on AWS
The following sections provide use cases for implementing MQTT topic best practices using AWS IoT.
MQTT command topics example
For a smart door lock application, a user must be able to submit a command to the lock that initiates a temporary key to be issued for an approved visitor. The temporary key consists of a TTL, code, and information about the authorized user.
The ability to create a temporary key allows another individual to open the lock for a specified period. This use case would apply in scenarios such as visiting family member arriving at the home while the primary owner is at work.
This scenario assumes the following details:
-
The homeowner has a mobile device ID of
mobile-1 -
The approved visitor has a mobile device ID of
mobile-2 -
The smart lock is installed as part of a group of other locks in the home. The set of locks has a context for
groupIdwheregroupIdequalsgroup-3 -
The smart lock for the front door has a
lockIdoflock-1 -
The smart lock hardware has a series number of
series100. The series is a unique identifier for this product version.
Command request to generate a smart lock code
The primary owner first publishes a command to the lock requesting a temporary access code created for an approved visitor. The command payload includes the identification of the homeowner’s mobile device, a randomly generated session identifier for tracking the current request, an action field that contains the type of command, and a topic field. The smart lock uses the topic in the topic field for publishing its response back to the homeowner.

Mobile user requests temporary credentials for the front door
Augment MQTT messages using any internal standards for requests, responses, and telemetry. For example, by adding in the requestor of the command in the payload, applications can specify different response topics based on the use case. If the homeowner requests a temporary lock but needs the response to reach all door locks in the home, the topic field could be changed to send to a group of devices.
Command processing on the smart lock
The smart lock receives the command message from the MQTT topic. By leveraging a consistent naming schema for commands in this application, the smart lock can ensure that it only receives commands on its specific command topic. This topic design also makes it possible for the lock to subscribe using a single level MQTT wildcard after its identifier.
The single level wildcard command is backward compatible as the IoT application adds new command types. The following example is a simplified example to show the topic structure. Consider using device attributes and policy variables restricting the topic(s) that a device can subscribe or publish to.

After receiving the MQTT payload, the smart lock parses the command request to determine what type of action to run. In this case, the command is related to credentials. The device also extracts the client ID, the session ID, and the response topic from the command payload.
Because a home can have multiple authorized homeowners, the client ID determines which homeowner has requested this change. In this example, the action field includes the type of credentials request, generate-password, and the associated user for the temporary key. Last, the device obtains the response topic field in the MQTT message and uses this information to publish its response.

Smart lock response published to AWS IoT Core
Command response delivered to the mobile client
The homeowner's mobile client subscribes to command responses for any smart locks in the group. Whenever the mobile client receives a successful command response, the temporary code along with any additional authorization permissions can be processed on the device and simultaneously stored in the AWS Cloud. Later, the authorized visitor can use the temporary code along with additional security credentials, such as exchanging for OAuth credentials, proving local presence to the door, and so on, to apply the temporary code to the smart lock.
In this workflow, the application used a command topic for a single device. However, a similar workflow may be used to request commands for multiple devices in a group, such as locking all of the doors in the home.

Command response sent from AWS IoT Core to mobile client
MQTT telemetry topics example
This section is an example of aggregating telemetry from a set of occupancy sensors that are placed throughout a building to monitor
room usage. The occupancy sensors communicate to a local gateway that is running
AWS IoT Greengrass
This scenario assumes the following details:
-
The occupancy sensors have IDs of
occupancy-1andoccupancy-2 -
The building is called
building-fresco -
Each sensor is placed on a specific floor and within a specific room name in
building-fresco. -
The AWS IoT Greengrass local gateway has a unique identifier of
gateway-1 -
The current building automation system correlates to an internal project called
acme
Local telemetry from occupancy sensor to AWS IoT Greengrass
Each occupancy sensor publishes an occupancy reading once per minute and whenever a person enters or leaves the room. Because the occupancy sensors do not correlate precisely to the state of the device and instead refer to the state of the room, the sensor publishes the room status on a telemetry topic. The payload includes a timestamp, occupancy count, and any efficiency countdown for turning off lights if a room is vacant. The occupancy sensor uses an MQTT topic that includes the contextual information about the position of the sensor within the building and its associated project. A AWS IoT Greengrass core receives all occupancy sensor data locally.

Local occupancy sensor publishes sensor reading to AWS IoT Greengrass
AWS IoT Greengrass telemetry from Edge to cloud
In this example, the primary role of AWS IoT Greengrass is to aggregate the data from multiple occupancy sensors then send the data to AWS IoT Core. Because AWS IoT Greengrass is the local bridge to the cloud, AWS IoT Greengrass adds metadata to each sensor reading.
AWS IoT Greengrass adds building information to each message to show the overall usage of the building in 5-minute
increments. AWS IoT Greengrass also augments the MQTT topic by including the appropriate application
identifier, acme.
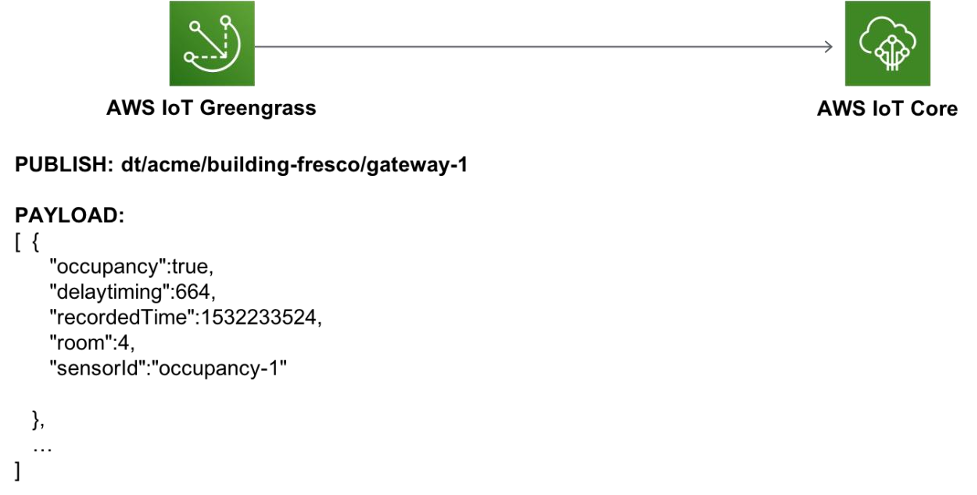
AWS IoT Greengrass aggregates and augments telemetry, then forwards messages to AWS IoT Core