Example 1: Bucket owner granting its users bucket permissions
Important
Granting permissions to IAM roles is a better practice than granting permissions to individual users.For more information about how to grant permissions to IAM roles, see Understanding cross-account permissions and using IAM roles.
Topics
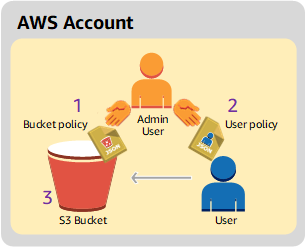
In this walkthrough, an AWS account owns a bucket, and the account includes an IAM user By default, the user has no permissions. For the user to perform any tasks, the parent account must grant them permissions. The bucket owner and parent account are the same. Therefore, to grant the user permissions on the bucket, the AWS account can use a bucket policy, a user policy, or both. The account owner will grant some permissions using a bucket policy and other permissions using a user policy.
The following steps summarize the walkthrough:
-
Account administrator creates a bucket policy granting a set of permissions to the user.
-
Account administrator attaches a user policy to the user granting additional permissions.
-
User then tries permissions granted via both the bucket policy and the user policy.
For this example, you will need an AWS account. Instead of using the root user credentials of the account, you will create an administrator user (see About using an administrator user to create resources and grant permissions). We refer to the AWS account and the administrator user as shown in the following table.
| Account ID | Account referred to as | Administrator user in the account |
|---|---|---|
|
|
Account A |
AccountAadmin |
Note
The administrator user in this example is AccountAadmin, which refers to Account A, and not AccountAdmin.
All the tasks of creating users and granting permissions are done in the AWS Management Console. To verify permissions, the walkthrough uses the command line tools, AWS Command Line Interface (AWS CLI) and AWS Tools for Windows PowerShell, so you don't need to write any code.
Preparing for the walkthrough
-
Make sure you have an AWS account and that it has a user with administrator privileges.
-
Sign up for an AWS account, if needed. We refer to this account as Account A.
-
Go to https://aws.amazon.com/s3
and choose Create an AWS account. -
Follow the on-screen instructions.
AWS will notify you by email when your account is active and available for you to use.
-
-
In Account A, create an administrator user
AccountAadmin. Using Account A credentials, sign in to the IAM consoleand do the following: -
Create user
AccountAadminand note the user security credentials.For instructions, see Creating an IAM user in your AWS account in the IAM User Guide.
-
Grant administrator privileges to AccountAadmin by attaching a user policy giving full access.
For instructions, see Managing IAM policies in the IAM User Guide.
-
Note the IAM user Sign-In URL for AccountAadmin. You will need to use this URL when signing in to the AWS Management Console. For more information about where to find the sign-in URL, see Sign in to the AWS Management Console as an IAM user in IAM User Guide. Note the URL for each of the accounts.
-
-
-
Set up either the AWS CLI or the AWS Tools for Windows PowerShell. Make sure that you save administrator user credentials as follows:
-
If using the AWS CLI, create a profile,
AccountAadmin, in the config file. -
If using the AWS Tools for Windows PowerShell, make sure you store credentials for the session as
AccountAadmin.
For instructions, see Setting up the tools for the walkthroughs.
-
Step 1: Create resources in Account A and grant permissions
Using the credentials of user AccountAadmin in Account A, and the special
IAM user sign-in URL, sign in to the AWS Management Console and do the following:
-
Create resources of a bucket and an IAM user
-
In the Amazon S3 console, create a bucket. Note the AWS Region in which you created the bucket. For instructions, see Creating a general purpose bucket.
-
In the IAM Console
, do the following: -
Create a user named Dave.
For step-by-step instructions, see Creating IAM users (console) in the IAM User Guide.
-
Note the
UserDavecredentials. -
Note the Amazon Resource Name (ARN) for user Dave. In the IAM Console
, select the user, and the Summary tab provides the user ARN.
-
-
-
Grant permissions.
Because the bucket owner and the parent account to which the user belongs are the same, the AWS account can grant user permissions using a bucket policy, a user policy, or both. In this example, you do both. If the object is also owned by the same account, the bucket owner can grant object permissions in the bucket policy (or an IAM policy).
-
In the Amazon S3 console, attach the following bucket policy to
awsexamplebucket1.The policy has two statements.
-
The first statement grants Dave the bucket operation permissions
s3:GetBucketLocationands3:ListBucket. -
The second statement grants the
s3:GetObjectpermission. Because Account A also owns the object, the account administrator is able to grant thes3:GetObjectpermission.
In the
Principalstatement, Dave is identified by his user ARN. For more information about policy elements, see Policies and permissions in Amazon S3. -
-
Create an inline policy for the user Dave by using the following policy. The policy grants Dave the
s3:PutObjectpermission. You need to update the policy by providing your bucket name.For instructions, see Managing IAMpolicies in the IAM User Guide. Note you need to sign in to the console using Account A credentials.
-
Step 2: Test permissions
Using Dave's credentials, verify that the permissions work. You can use either of the following two procedures.
Test permissions using the AWS CLI
-
Update the AWS CLI config file by adding the following
UserDaveAccountAprofile. For more information, see Setting up the tools for the walkthroughs.[profile UserDaveAccountA] aws_access_key_id =access-keyaws_secret_access_key =secret-access-keyregion =us-east-1 -
Verify that Dave can perform the operations as granted in the user policy. Upload a sample object using the following AWS CLI
put-objectcommand.The
--bodyparameter in the command identifies the source file to upload. For example, if the file is in the root of the C: drive on a Windows machine, you specifyc:\HappyFace.jpg. The--keyparameter provides the key name for the object.aws s3api put-object --bucketawsexamplebucket1--keyHappyFace.jpg--bodyHappyFace.jpg--profile UserDaveAccountARun the following AWS CLI command to get the object.
aws s3api get-object --bucket awsexamplebucket1 --keyHappyFace.jpgOutputFile.jpg--profile UserDaveAccountA
Test permissions using the AWS Tools for Windows PowerShell
-
Store Dave's credentials as
AccountADave. You then use these credentials toPUTandGETan object.set-awscredentials -AccessKeyAccessKeyID-SecretKeySecretAccessKey-storeas AccountADave -
Upload a sample object using the AWS Tools for Windows PowerShell
Write-S3Objectcommand using user Dave's stored credentials.Write-S3Object -bucketnameawsexamplebucket1-keyHappyFace.jpg-fileHappyFace.jpg-StoredCredentials AccountADaveDownload the previously uploaded object.
Read-S3Object -bucketnameawsexamplebucket1-keyHappyFace.jpg-fileOutput.jpg-StoredCredentials AccountADave