What is Nitro Enclaves?
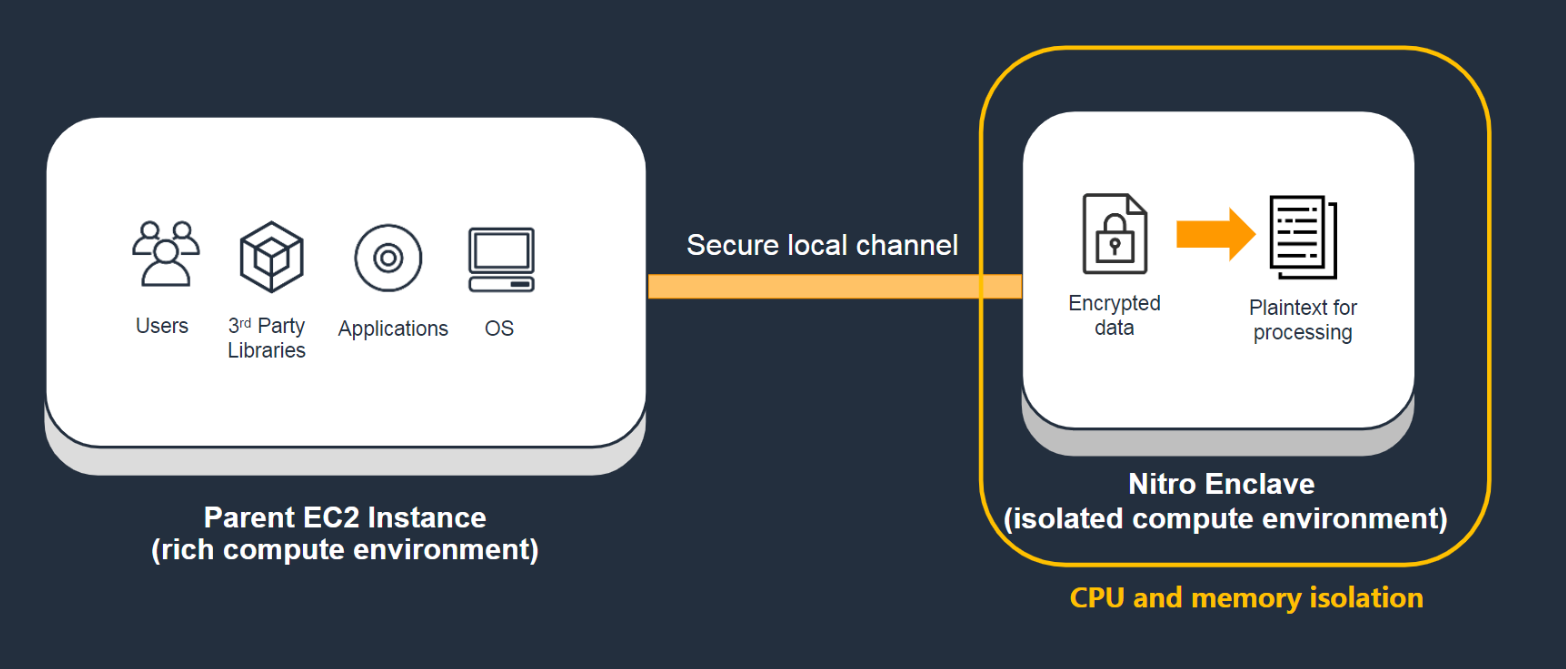
AWS Nitro Enclaves is an Amazon EC2 feature that allows you to create isolated execution environments, called enclaves, from Amazon EC2 instances. Enclaves are separate, hardened, and highly-constrained virtual machines. They provide only secure local socket connectivity with their parent instance. They have no persistent storage, interactive access, or external networking. Users cannot SSH into an enclave, and the data and applications inside the enclave cannot be accessed by the processes, applications, or users (root or admin) of the parent instance. Using Nitro Enclaves, you can secure your most sensitive data, such as personally identifiable information (PII), and your data processing applications.
Note
Nitro Enclaves is processor agnostic and it is supported on most Intel, AMD, and AWS Graviton-based Amazon EC2 instance types built on the AWS Nitro System.
Nitro Enclaves also supports an attestation feature, which allows you to verify an enclave's identity and ensure that only authorized code is running inside it. Nitro Enclaves is integrated with the AWS Key Management Service, which provides built-in support for attestation and enables you to prepare and protect your sensitive data for processing inside enclaves. Nitro Enclaves can also be used with other key management services.
Nitro Enclaves use the same Nitro Hypervisor technology that provides CPU and memory isolation for Amazon EC2 instances in order to isolate the vCPUs and memory for an enclave from a parent instance. The Nitro Hypervisor ensures that the parent instance has no access to the isolated vCPUs and memory of the enclave.
To learn more about creating your first enclave using a sample enclave application, see Getting started with the Hello Enclaves sample application.
Learn more
-
To learn about the concepts used in Nitro Enclaves, see Nitro Enclaves concepts.
-
To get started with your first enclave using a sample enclave application, see Getting started with the Hello Enclaves sample application.
-
To learn about using the AWS Nitro Enclaves CLI to manage the lifecycle of enclaves, see Nitro Enclaves Command Line Interface.
-
To learn about developing custom enclave applications and the AWS Nitro Enclaves SDK, see Nitro Enclaves application development.
-
To learn about multiple enclaves, see Working with multiple enclaves.
Requirements
Nitro Enclaves has the following requirements:
-
Parent instance requirements:
-
Virtualized Nitro-based instances
-
Intel or AMD-based instances with at least 4 vCPUs, except:
c7i.16xlarge|c7i.24xlarge|c7i.48xlarge|c7i-flex.*|g4ad.*|hpc6a.*|hpc6id.*|hpc7a.*|i7i.16xlarge|i7i.24xlarge|i7i.48xlarge|i7ie.18xlarge|i7ie.24xlarge|i7ie.48xlarge|m7i.16xlarge|m7i.24xlarge|m7i.48xlarge|m7i-flex.*|p6-b200.*|r7i.16xlarge|r7i.24xlarge|r7i.48xlarge|r7iz.16xlarge|r7iz.32xlarge|t3.*|t3a.*|u-*|u7i-*|vt1.*. -
AWS Graviton-based instances with at least 2 vCPUs, except:
a1.*|c7gn.*|g5g.*|hpc7g.*|im4gn.*|is4gen.*|t4g.*.
-
-
Linux or Windows (2016 or later) operating system
-
-
Enclave requirements:
-
Linux operating system only
-
Considerations
Keep the following in mind when using Nitro Enclaves:
-
Nitro Enclaves is supported in the following Regions: US East (Ohio), US East (N. Virginia), US West (N. California), US West (Oregon), Africa (Cape Town), Asia Pacific (Hong Kong), Asia Pacific (Hyderabad), Asia Pacific (Jakarta), Asia Pacific (Mumbai), Asia Pacific (Osaka), Asia Pacific (Seoul), Asia Pacific (Singapore), Asia Pacific (Sydney), Asia Pacific (Tokyo), Canada (Central), Europe (Frankfurt), Europe (Ireland), Europe (London), Europe (Milan), Europe (Paris), Europe (Stockholm), Middle East (Bahrain), South America (São Paulo), AWS GovCloud (US-East), and AWS GovCloud (US-West).
-
You can create up to four individual enclaves per parent instance.
-
Enclaves can communicate only with the parent instance. Enclaves running on the same or different parent instances cannot communicate with each other.
-
Enclaves are active only while their parent instance is in the
runningstate. If the parent instance is stopped or terminated, its enclaves are terminated. -
You cannot enable hibernation and enclaves on the same instance.
-
Nitro Enclaves is not supported on Outposts.
-
Nitro Enclaves is not supported in Local Zones or Wavelength Zones.
Pricing
There are no additional charges for using Nitro Enclaves. You are billed the standard charges for the Amazon EC2 instance and for the other AWS services that you use.
Related services
Nitro Enclaves is integrated with the following AWS services:
- AWS Key Management Service
-
AWS Key Management Service (KMS) makes it easy for you to create and manage cryptographic keys and control their use across a wide range of AWS services and in your applications. Nitro Enclaves integrates with AWS KMS and it allows you to perform selected KMS operations from the enclave using the AWS Nitro Enclaves SDK
. These operations can be tied to the cryptographic attestation process of Nitro Enclaves by setting a AWS KMS key policy to ensure that the operation works only when the measurements of the enclave match the KMS key policy. For more information, see AWS KMS condition keys for Nitro Enclaves in the AWS Key Management Service Developer Guide. - AWS Certificate Manager
-
AWS Certificate Manager (ACM) is a service that lets you easily provision, manage, and deploy public and private Secure Sockets Layer/Transport Layer Security (SSL/TLS) certificates for use with AWS services and your internal connected resources. SSL/TLS certificates are used to secure network communications and to establish the identity of websites over the internet, as well as resources on private networks. ACM removes the time-consuming manual process of purchasing, uploading, and renewing SSL/TLS certificates. For more information, see AWS Certificate Manager for Nitro Enclaves.