Building a landing zone
You have a few options for creating your landing zone on AWS. You can choose a managed
service to orchestrate your environment or work with a partner to build your own. AWS offers
AWS Control Tower
Options for landing zones on AWS:
-
AWS Control Tower
-
Custom-built landing zone
Delivery mechanism:
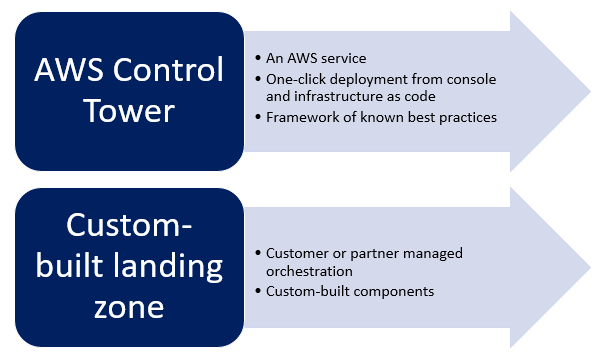
Benefits and trade-offs for each approach:
| Solution | Benefits | Trade-offs |
|---|---|---|
|
AWS Control Tower |
|
|
|
AWS Organizations |
|
|
All multi-account environment offerings are powered by AWS Organizations. AWS Organizations provides the underlying infrastructure and capabilities for you to build and manage your AWS environment. With AWS Organizations, you can take the multi-account strategy guidance provided by AWS and customize your environment yourself to best fit your business needs. If you are an existing customer and you’re happy with your current AWS Organizations implementation, you should continue to operate your current AWS environment.
AWS Control Tower
AWS Control Tower runs as an AWS managed service. When you’re looking for a pre-packaged environment solution out of the box, you can use AWS Control Tower for prescriptive guidance and a fully managed environment. The service sets up a landing zone based on multi-account best practices, centralizes identity and access management, and establishes pre-configured governance rules for security and compliance.
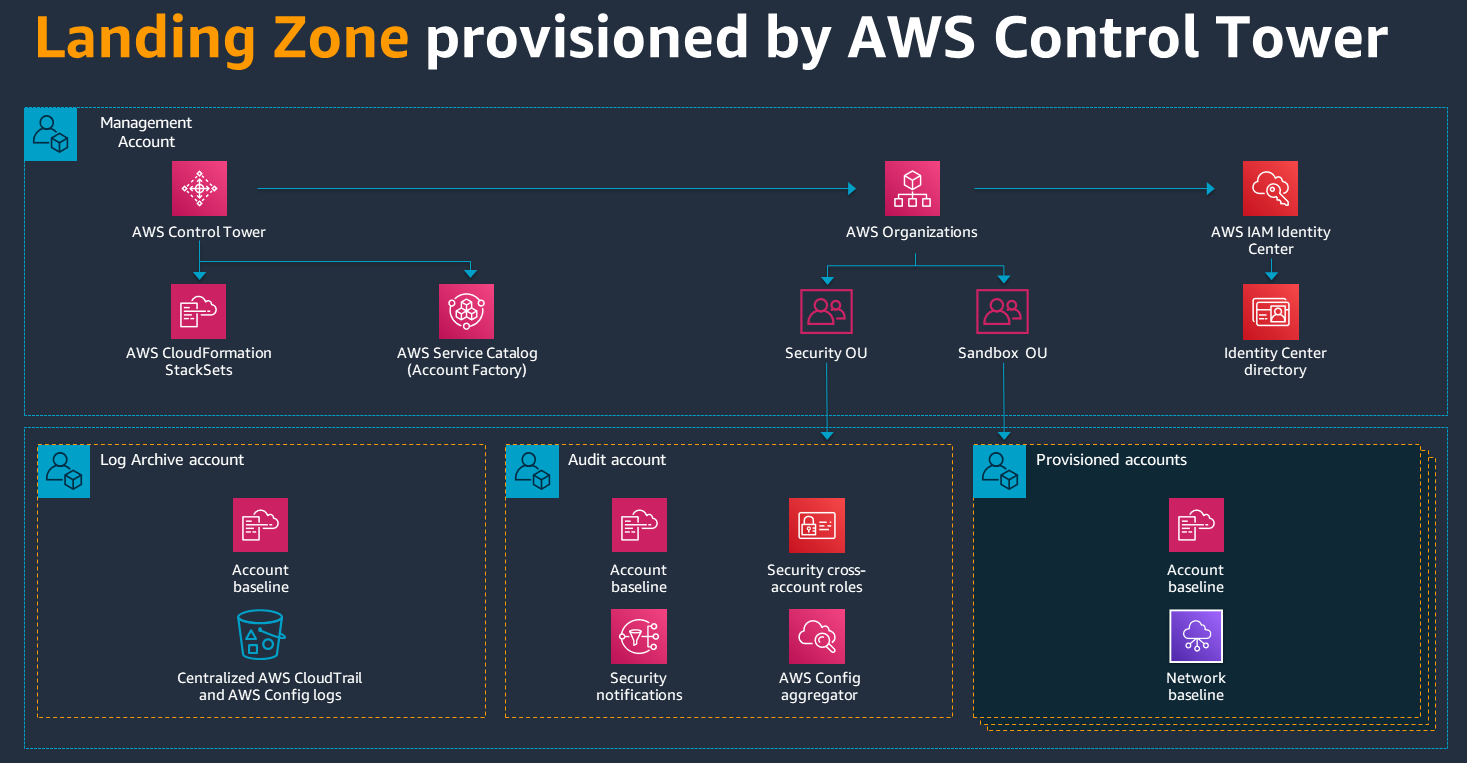
AWS Control Tower automates the setup of a new landing zone by using best practices, blueprints for identity, federated access, and account structure. Some of the blueprints implemented on AWS Control Tower include:
-
A multi-account environment using AWS Organizations
-
Cross-account security audits using AWS Identity and Access Management (IAM) and AWS IAM Identity Center
-
Identity management using the Identity Center default directory
-
Centralized logging from AWS CloudTrail, and AWS Config stored in Amazon Simple Storage Service (Amazon S3)
Controls are high-level rules that provide ongoing governance for your overall AWS environment. Controls can be preventive or detective. Preventive controls are implemented by using service control policies (SCPs), which are a part of AWS Organizations. Detective controls are implemented by using AWS Config. Examples of AWS Control Tower controls include:
-
Disallow creation of access keys for the root user
-
Disallow internet connection through RDP
-
Disallow public write access to S3 buckets
-
Disallow Amazon Elastic Block Store (Amazon EBS) volumes that are unattached to an Amazon Elastic Compute Cloud (Amazon EC2) instance
Note
AWS Control Tower is a starting point for a landing zone. You need to determine your strategy for networking, access management, and security based on your unique requirements as you build out your landing zone.
Custom-built landing zone
You can choose to build your own customized landing zone solution. In this case, you implement the baseline environment to get started with identity and access management, governance, data security, network design, and logging. We recommend this approach if you want to build all of your environment components from scratch, or if you have requirements that only a custom solution can support. You must have enough expertise in AWS to manage, upgrade, maintain, and operate the solution once it’s deployed.
Recommended approach
We recommend that you start with AWS Control Tower to build your landing zone. AWS Control Tower helps you build out an initial prescriptive landing zone configuration, use out-of-the-box controls and blueprints, and create new accounts by using AWS Control Tower Account Factory.
During setup, you can customize your landing zone from the AWS Control Tower console. For details, see the AWS Control Tower documentation. After you set up your foundational landing zone, use one of these options to enhance and customize it further:
-
Use Customizations for AWS Control Tower (CfCT), which provides extensive customization options through AWS CloudFormation templates and service control policies (SCPs). For more information, see the AWS Control Tower documentation.
-
Use the Landing Zone Accelerator (LZA) to enhance your landing zone to align with compliance frameworks. For more information, see the LZA implementation guide.