Set up DNS resolution for hybrid networks in a multi-account AWS environment
Created by Amir Durrani
Environment: Production | Technologies: Infrastructure; Networking | AWS services: AWS RAM; Amazon Route 53; AWS Control Tower |
Summary
This pattern describes how you can use on-premises Domain Name System (DNS) services with Amazon Route 53 Resolver rules and outbound Resolver endpoints for name resolution.
DNS is fundamental to establishing and maintaining communications across network environments. If you have a hybrid network connectivity environment, you can share critical network services such as DNS and Active Directory without the operational burden of managing a distributed environment across accounts and virtual private clouds (VPCs). This approach helps you build and support applications that span a large number of accounts. For example, if you have hundreds or thousands of multi-Region accounts with hybrid connectivity requirements, you can share DNS services securely and efficiently across all connected environments within your AWS organization.
DNS is critical to IP networking among all tiers (web, application, and database) of an application. It is best practice to give only the team of DNS experts full access to configure, operate, and support this resource. In a hybrid connectivity environment, you can continue to use your on-premises DNS for name resolution requests originating from resources that reside in different accounts, by using conditional forwarding.
This pattern covers hybrid DNS resolution in an AWS multi-account environment. For single accounts, see the pattern Set up DNS resolution for hybrid networks in a single-account AWS environment.
Prerequisites and limitations
Prerequisites
An AWS multi-account environment that is based on best practices and built by using AWS Control Tower. The diagram in the next section shows the typical architecture of such an environment.
Scalable routing infrastructure between the accounts and VPCs by using AWS Transit Gateway.
Outbound Resolver endpoints and Resolver rules by using Amazon Route 53.
Resource shares for outbound Resolver rules by using AWS Resource Access Manager (AWS RAM).
Architecture
AWS multi-account architecture
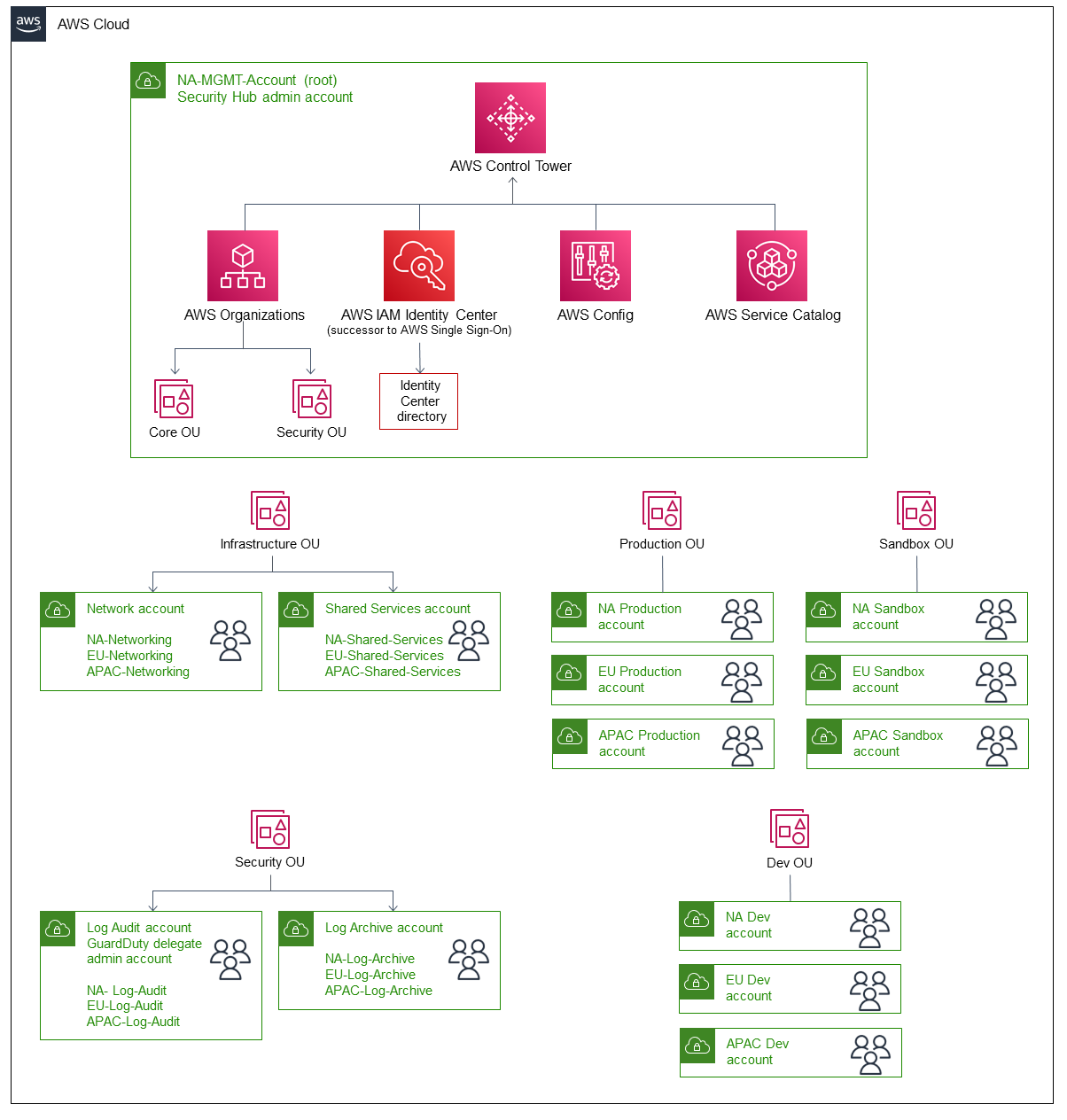
Target technology stack
An existing on-premises DNS infrastructure for outbound name resolution across a large number of AWS principals
Route 53 Resolver rule and outbound Resolver endpoints
AWS RAM for sharing Route 53 Resolver rules with other AWS principals within and outside the AWS organization
Target architecture
The following diagram depicts the steps for configuring the end-to-end hybrid DNS resolution. AWS RAM is used to share the Route 53 Resolver rules and Resolver endpoints, which are configured and managed from the central Shared Services account. Route 53 Resolver endpoints are configured for each Availability Zone to receive the outbound name resolution requests for the resources that reside in the on-premises data center, and to then forward these requests to the on-premises DNS resolvers. The on-premises DNS resolvers send the name resolution responses to the outbound endpoints, which then forward the responses to the VPC resolver. These steps establish end-to-end communication by using hostnames instead of IP addresses.
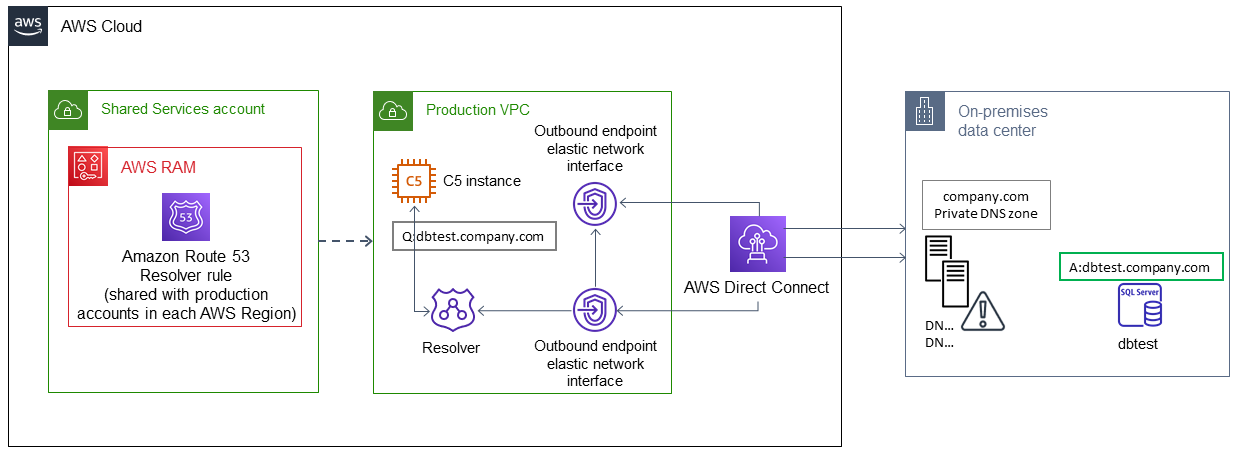
The following diagram shows the architecture in more detail.

Automation and scale
You can configure and share Route 53 Resolver rules through AWS RAM by using AWS CloudFormation templates.
Tools
AWS services
AWS Control Tower helps you set up and govern an AWS multi-account environment, following prescriptive best practices.
AWS Resource Access Manager (AWS RAM) helps you securely share your resources across AWS accounts to reduce operational overhead and provide visibility and auditability.
Amazon Route 53 is a highly available and scalable DNS web service.
Additional tools
nslookup and dig are utilities for querying DNS records.
Epics
| Task | Description | Skills required |
|---|---|---|
Configure Route 53 outbound Resolver endpoints and rules. |
For more information, see Forwarding outbound DNS queries to your network in the Route 53 documentation. | General AWS |
Create and share Route 53 outbound Resolver rules with AWS principals. |
For more information, see Sharing your AWS resources in the AWS RAM documentation. | General AWS |
Test the outbound DNS name resolution. | Test the name resolution by using the nslookup or dig utility on instances in a VPC in an account that you have shared the Resolver rule with. The query should resolve to the IP address of a resource that resides within your on-premises data center. | General AWS |
Related resources
Forwarding outbound DNS queries to your network (Route 53 documentation)
Sharing your AWS resources (AWS RAM documentation)