Automatically encrypt existing and new Amazon EBS volumes
Tony DeMarco and Josh Joy, Amazon Web Services
Summary
Encryption of Amazon Elastic Block Store (Amazon EBS) volumes is important to an organization's data protection strategy. It is an important step in establishing a well-architected environment. Although there is no direct way to encrypt existing unencrypted EBS volumes or snapshots, you can encrypt them by creating a new volume or snapshot. For more information, see Encrypt EBS resources in the Amazon EC2 documentation. This pattern provides preventative and detective controls for encrypting your EBS volumes, both new and existing. In this pattern, you configure account settings, create automated remediation processes, and implement access controls.
Prerequisites and limitations
Prerequisites
An active Amazon Web Services (AWS) account
AWS Command Line Interface (AWS CLI), installed and configured on macOS, Linux, or Windows
jq
, installed and configured on macOS, Linux, or Windows AWS Identity and Access Management (IAM) permissions are provisioned to have read and write access to AWS CloudFormation, Amazon Elastic Compute Cloud (Amazon EC2), AWS Systems Manager, AWS Config, and AWS Key Management Service (AWS KMS)
AWS Organizations is configured with all features enabled, a requirement for service control policies
AWS Config is enabled in the target accounts
Limitations
In your target AWS account, there must be no AWS Config rules named encrypted-volumes. This solution deploys a rule with this name. Preexisting rules with this name can cause the deployment to fail and result in unnecessary charges related to processing the same rule more than once.
This solution encrypts all EBS volumes with the same AWS KMS key.
If you enable encryption of EBS volumes for the account, this setting is Region-specific. If you enable it for an AWS Region, you cannot disable it for individual volumes or snapshots in that Region. For more information, see Encryption by default in the Amazon EC2 documentation.
When you remediate existing, unencrypted EBS volumes, ensure that the EC2 instance is not in use. This automation shuts down the instance in order to detach the unencrypted volume and attach the encrypted one. There is downtime while the remediation is in progress. If this is a critical piece of infrastructure for your organization, make sure that manual or automatic high-availability configurations are in place so as to not impact the availability of any applications running on the instance. We recommend that you remediate critical resources only during standard maintenance windows.
Architecture
Automation workflow
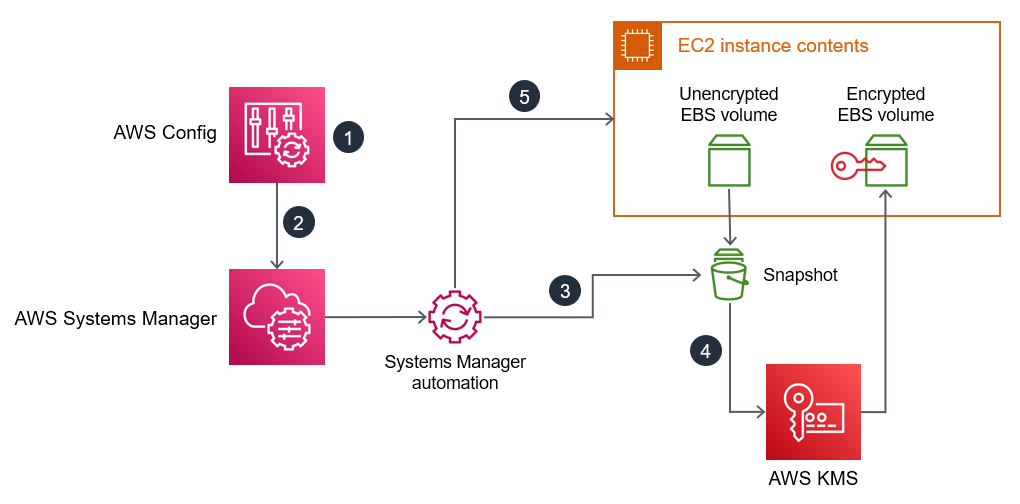
AWS Config detects an unencrypted EBS volume.
An administrator uses AWS Config to send a remediation command to Systems Manager.
The Systems Manager automation takes a snapshot of the unencrypted EBS volume.
The Systems Manager automation uses AWS KMS to create an encrypted copy of the snapshot.
The Systems Manager automation does the following:
Stops the affected EC2 instance if it is running
Attaches the new, encrypted copy of the volume to the EC2 instance
Returns the EC2 instance to its original state
Tools
AWS services
AWS CLI – The AWS Command Line Interface (AWS CLI) provides direct access to the public application programming interfaces (APIs) of AWS services. You can explore a service's capabilities with the AWS CLI and develop shell scripts to manage your resources. In addition to the low-level API-equivalent commands, several AWS services provide customizations for the AWS CLI. Customizations can include higher-level commands that simplify using a service with a complex API.
AWS CloudFormation – AWS CloudFormation is a service that helps you model and set up your AWS resources. You create a template that describes all the AWS resources that you want (such as Amazon EC2 instances), and CloudFormation provisions and configures those resources for you.
AWS Config – AWS Config provides a detailed view of the configuration of AWS resources in your AWS account. This includes how the resources are related to one another and how they were configured in the past so that you can see how the configurations and relationships change over time.
Amazon EC2 – Amazon Elastic Compute Cloud (Amazon EC2) is a web service that provides resizable computing capacity that you use to build and host your software systems.
AWS KMS – AWS Key Management Service (AWS KMS) is an encryption and key management service scaled for the cloud. AWS KMS keys and functionality are used by other AWS services, and you can use them to protect data in your AWS environment.
AWS Organizations – AWS Organizations is an account management service that enables you to consolidate multiple AWS accounts into an organization that you create and centrally manage.
AWS Systems Manager Automation – Systems Manager Automation simplifies common maintenance and deployment tasks for Amazon EC2 instances and other AWS resources.
Other services
jq
– jq is a lightweight and flexible command-line JSON processor. You use this tool to extract key information from the AWS CLI output.
Code
The code for this pattern is available in the GitHub Automatically remediate unencrypted EBS Volumes using customer KMS keys
repository.
Epics
| Task | Description | Skills required |
|---|---|---|
Download scripts and CloudFormation templates. | Download the shell script, JSON file, and CloudFormation templates from the GitHub Automatically remediate unencrypted EBS Volumes using customer KMS keys | AWS administrator, General AWS |
Identify the administrator for the AWS KMS key. |
| AWS administrator, General AWS |
Deploy the Stack1 CloudFormation template. |
For more information about deploying a CloudFormation template, see Working with AWS CloudFormation templates in the CloudFormation documentation. | AWS administrator, General AWS |
Deploy the Stack2 CloudFormation template. | In CloudFormation, deploy the
| AWS administrator, General AWS |
Create an unencrypted volume for testing. | Create an EC2 instance with an unencrypted EBS volume. For instructions, see Create an Amazon EBS volume in the Amazon EC2 documentation. The instance type does not matter, and access to the instance is not needed. You can create a t2.micro instance to stay in the free tier, and you don’t need to create a key pair. | AWS administrator, General AWS |
Test the AWS Config rule. |
You can view the remediation progress and status in Systems Manager as follows:
| AWS administrator, General AWS |
Configure additional accounts or AWS Regions. | As needed for your use case, repeat this epic for any additional accounts or AWS Regions. | AWS administrator, General AWS |
| Task | Description | Skills required |
|---|---|---|
Run the enable script. |
| AWS administrator, General AWS, bash |
Confirm the settings are updated. |
| AWS administrator, General AWS |
Configure additional accounts or AWS Regions. | As needed for your use case, repeat this epic for any additional accounts or AWS Regions. | AWS administrator, General AWS |
| Task | Description | Skills required |
|---|---|---|
Create a service control policy. |
| AWS administrator, General AWS |
Related resources
AWS service documentation
Other resources
jq manual
(jq website) jq download
(GitHub)